PAM, an extension of Identity Access Management to combat cyber attacks involving the theft of sensitive credentials
While servers are, on the whole, increasingly secure against intrusion, the theft of login credentials (login/password) has become one of the preferred attack vectors used by cybercriminals to corrupt a machine and gain fraudulent access to an information system. This is achieved by elevating the privileges of the usurped account, thanks to software vulnerabilities, making it possible to bounce from one machine to another and gain access to the most sensitive data, or to disable a company's IS.
Cybercriminals are particularly targeting access to servers and applications shared with partners, or retained by an employee after leaving the company. While access to the corporate network is often secured by a VPN (Virtual Private Network), access to the machines themselves is still too often via a generic account, shared by all users - internal and external to the company - with administrative rights. And yet, once inside a company network, it's easy to bounce from one server to another. This "lightness" has been pointed out by the ANSSI, which recommends in its IT hygiene guide that these privileged accesses should be more closely controlled, to give everyone access to the IS in proportion to their strict needs.
Privileged Access Management
To remedy this potential flaw, the best practice is to set up a "Bastion" or PAM.
It allows you to :
- Give each user access, possibly temporary, to the machines / web consoles they need to work. And not to the whole network, as a VPN allows;
- Enhance security with strong authentication ;
- Manage access rights with user-specific login credentials;
- track accesses and actions carried out on machines.
Scalair now offers this type of solution in as-a-service mode, with the Bastion managed service.
PAM: Regain control of administrator access
Today's information systems are increasingly large. They include numerous servers and applications, and just as many administrators, both internal to the company (on-site or telecommuting) and external. Starting with application partners, who need access to machines to deploy, maintain and update their software. Yet no one can verify the level of security guaranteed by each of these partners. For example, the security measures put in place to protect login credentials or prevent the compromise or theft of their employees' workstations, or data theft through phishing or the exploitation of vulnerabilities.

By securing access to machines/applications using a single VPN + generic login credentials, it is impossible to restrict an administrator's or partner's access perimeter, define an access time slot, track and control their actions, or revoke a user's access without renewing a login credential kept hard-coded on the machine, potentially used by several people. In other words, by granting network access to your partners, you leave an open door to your information system.
The PAM by Scalair solution offers precisely these functions, by interposing itself between users with privileged access and the company's infrastructure (hosted by Scalair or elsewhere). The principle of the solution is to create a unique internal or partner admin account for each user, and to associate authorized targets (servers/web applications) with it, via IS system accounts that remain unknown to administrators.

Customization & Features
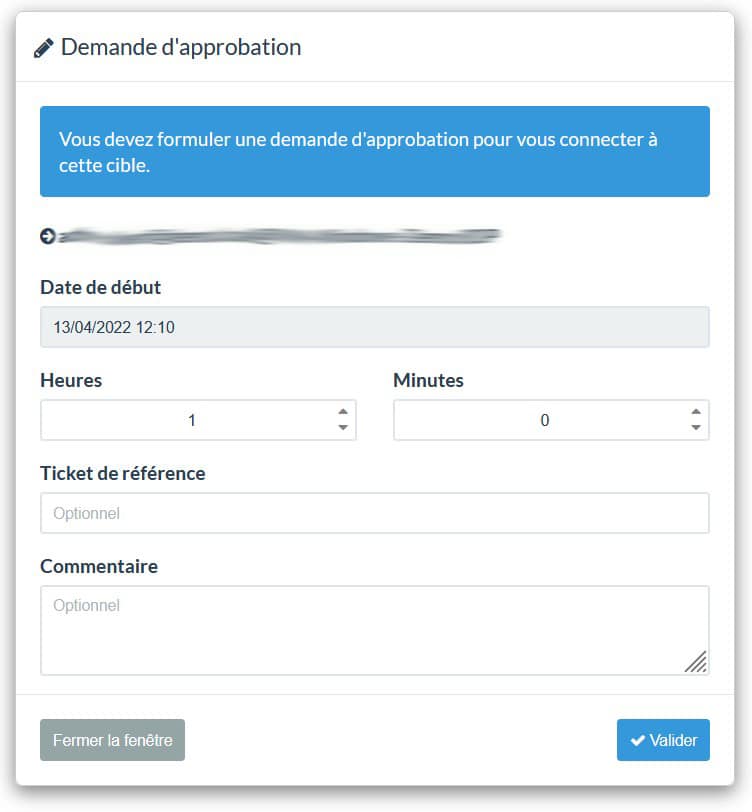
You can then add connection restrictions (with or without the need for prior approval). You can also activate double authentication, natively available via a mobile application generating a code on the user's phone. What's more, all accesses are tracked and time-stamped, and the actions performed by the user are visible in real time to a "super administrator" in the role of "auditor". Either via video (RDP remote desktop), or via command lines entered, depending on the protocol used. These logs and files are kept for a retention period of one year, in compliance with current regulations. They can be used to trace the origin of a security incident or malfunction caused by an update or production start-up.
The listener can also close a session with a single click.
Illustrate the points raised with a gallery of captioned screenshots.
A turnkey solution, accessible to SMEs and large groups alike, based on Wallix software from France
Scalair's PAM as a service solution is based on Wallix software, developed in France. It is hosted by Scalair, on a high-availability architecture consisting of two virtual machines. The security of these machines, and any scalability requirements, are managed entirely by the Scalair team.
The service commitment associated with this offer is a guarantee of peace of mind for customers. They can rely on Scalair to deploy, configure and maintain this solution, which is a key component of their information system.
For their part, customers simply need to provide an exhaustive list of privileged accounts and associated rights. They then access the solution via a simple, easy-to-read web interface, requiring no advanced skills. And there's no need for a VPN, since every administrator has access to the web servers/consoles he or she needs.
To make this solution accessible to as many people as possible, the price comes with no surprises and no time commitment.
The price varies according to the number of simultaneous connections required. However, there is no limit on the number of servers/applications, unlike other competing offers.
The monthly subscription includes: the license, deployment and hosting of the solution, its management and support.
Don't forget the organizational challenges of such a project!
Relying on Scalair for the technical implementation of a PAM project will enable you to focus, with our support, on the organizational challenges that arise from such a project. After all, the habits of your staff and partners will obviously have to change. And some of them are bound to point to new constraints. You'll need to explain why this revolution is necessary, and put the right processes in place. In particular, you'll need to ensure that your IT team is reactive when notified of a request for approval, for example!
